You can create Permission Policies for your Users and assign these Permission Policies to them. There are two types of Permission Policies you can assign to Users:Documentation Index
Fetch the complete documentation index at: https://docs.m3ter.com/llms.txt
Use this file to discover all available pages before exploring further.
- Custom. The policies you create yourself for controlling access to your Organization.
- Managed. System generated policies which you can assign to Users but which you cannot edit to change the access to resources they are configured to allow or deny.
- Understanding the m3ter Permissions Model
- Permission Policy Statements - Actions and Resources
- Creating a Custom Permission Policy
- Permissions Exceptions
Understanding the m3ter Permissions Model
The m3ter Permissions model is implemented using a three-fold framework of Effect, Action, and Resource:- Def: A Permission is defined as imposing an effect of either allowing or denying access to a specific resource to perform a specific action on that resource.
Resources
Resources are defined as m3ter Resource Identifiers (MRIs) in the format:
service:resource-type/item-type/id
Where:
- service is a distinct part of the overall m3ter system, and which forms a natural functional grouping, such as “config” or “billing”.
- resource-type is the resource type item accessed - for example: “Plan”, “Meter”, “Bill”
-
item-type is one of:
- “item” - to specify an individual item.
- “group” - to specify a resource group.
- id is the resource group id or the resource item id
- To denote as resource a specific Plan with an id = 12345 in the config service, the MRI would be:
config:plan/item/12345
- To denote as resource a Plan Resource Group with id= 987 (that is, applying to all Plans that are contained within the resource group) the MRI would be:
config:plan/group/987
Use of Wildcards for Resources
The use of wildcards when denoting resources is allowed. For example, to denote all Plans as the resource in a permission statement, you can use:
config:plan/*
Resource Groups
Resources can be assigned to one or more Resource Groups. For example, a Plan can be assigned to Plan Resource Groups, a Meter can be assigned to Meter Resource Groups, and so on. This is useful for cases where you want to create Permission Policies which allow or deny access to a specific subset of resources - you want to grant access to a User to only some of the Plans in your Organization. This concept of grouping resources applies to every resource in m3ter, including Resource Groups themselves, which allows you to nest resource groups to support hierarchies of groups.Actions
Actions define what a User is either allowed or not allowed to do with respect to a resource. For example, you can use aconfig:create and config:retrieve action to create a statement for a Permission Policy that allows Users to create or retrieve any Plan in your Organization. But if this is the only Permission Policy assigned to a User, they will not be able to update or delete any Plans:
Effects and Evaluation Logic
The effect for a Permission Policy is either to allow or to deny:- Allow - indicates the policy is allowing access to the resource(s) for the given action(s).
- Deny - indicates the policy is denying access to the resource(s) for the given action(s).
-
There is an implicit denial - the order of evaluation is:
- We check to see if there is a statement that denies access to a resource for a given action. If there is, the access is denied.
- We check to see if there is a statement that allows access to a resource for a given action. If there is, the access is allowed.
- If there is no statement that explicitly denies and no statement that explicitly allows, the access is denied.
-
In the case of a conflict of deny/allow, denial takes precedence:
- If there is a statement that denies access to a resource for a given action and there is a statement that allows access to a resource for the same action, the access is denied.
Permission Policy Statements - Available Actions and Resources
This section lists the actions and resources available for compiling statements you add to your custom Permission Policies.Statements - Available Actions
When creating statements for Permission Policies, actions always require a resource-type to operate against. Some actions also require a resource path - either a specific item or group to be defined or a wildcard‘*' to indicate all items of the resource-type.
For a config:create action, no resource path is required and we use a wildcard to apply denial of meter creation to all meters:
config:retrieve action, a resource path is required:
| Action | MRI Path Required? |
|---|---|
| config:create | No |
| config:retrieve | Yes |
| config:update | Yes |
| config:delete | Yes |
| measurements:upload | Yes |
| measurements:fileUpload | Yes |
| measurements:retrieve | Yes |
| exports:download | Yes |
| ALL | * |
Which Actions can I use with which Resources?
For the resources listed in the following section, the Actions you can use when creating Permission Policy Statements are determined by Resource type:-
Measurements data:
measurements:retrievemeasurements:uploadmeasurements:fileUpload
-
Exports data:
exports:download
-
Other Resource types:
config:createconfig:retrieveconfig:updateconfig:delete
Examples
- Billing Operations. Suppose you want to set up a Permission Policy that you’ll assign to Users of your Organization that belong to the Billing Operations Team. You want them to have full access to work with a specific collection of Bill, Account, AccountPlan, and Bill Statement resources. You can use the four
configactions with the relevant resources to build the required Permission Policy statement:
- Measurements Data. For a Permission Policy statement you want to use to define User permissions for the
measurements:dataresource, you cannot use any of theconfigactions. If you want to create a Permission Policy to allow a User full access to work with measurements data, you must use themeasurementsactions:
- Data Exports. For a Permission Policy granting Users full working access to create, manage and run data exports, you can create a Permission Policy with two statements. To create and manage data exports:
- To run data exports:
Statements - Available Resources
You can use the following resources when creating Permission Policy statements:| Resource | Policy Statement Format |
|---|---|
| ALL | * |
| action | |
| ACTION_PERFORMED | action:actionPerformed |
| analytics | |
| USAGE | analytics:usage |
| billing | |
| BALANCE | billing:balance |
| BILL | billing:bill |
| BILL_JOB | billing:billjob |
| CHARGE | billing:charge |
| BILL_CONFIG | billing:config |
| COUNTER_ADJUSTMENT | billing:counterAdjustment |
| CREDIT | billing:credit |
| CREDIT_ADJUSTMENT | billing:creditAdjustment |
| BILL_LOCK | billing:lock |
| SCHEDULED_VALIDATION | billing:validation |
| config | |
| ACCOUNT | config:account |
| ACCOUNT_PLAN | config:accountPlan |
| ACTION | config:action |
| ACTION_TRIGGER | config:actionTrigger |
| AGGREGATION | config:aggregation |
| ALERT | config:alert |
| ANALYTICS_JOB | config:analyticsJob |
| COMMITMENT | config:commitment |
| CONTRACT | config:contract |
| COUNTER | config:counter |
| PICKLIST_CREDIT_REASON | config:creditReason |
| CREDIT_TYPE | config:creditType |
| PICKLIST_CURRENCY | config:currency |
| CUSTOM_FIELD | config:customField |
| DATA_EXPLORER_SELECTION | config:dataExplorerSelection |
| PICKLIST_DEBIT_REASON | config:debitReason |
| EVENT | config:event |
| EXTERNAL_MAPPING | config:externalMapping |
| INTEGRATION | config:integration |
| METER | config:meter |
| METER_GROUP | config:metergroup |
| NOTIFICATION | config:notification |
| ORGANIZATION_CONFIG | config:organizationConfig |
| OUTGOING_INTEGRATION | config:outgoingIntegration |
| PERMISSION_POLICY | config:permissionPolicy |
| PRINCIPAL_PERMISSION | config:principalPermission |
| PLAN | config:plan |
| PLAN_GROUP | config:planGroup |
| PLAN_GROUP_LINK | config:planGroupLink |
| PLAN_TEMPLATE | config:planTemplate |
| PRODUCT | config:product |
| REPORT_SELECTION | config:reportSelection |
| RESOURCE_GROUP | config:resourceGroup |
| SERVICE_USER | config:serviceUser |
| SUPPORT_USERS | config:supportUsers |
| TEMPLATE | config:template |
| PICKLIST_TRANSACTION_TYPE | config:transactionType |
| ORG_USER | config:user |
| ORG_USER_INVITATION | config:orgUserInvitation |
| EXPORT_DESTINATION | config:exportDestination |
| EXPORT_SCHEDULES | config:exportSchedules |
| EXPORT_STATUS | config:exportStatus |
| SCHEDULED_EVENT | config:scheduledEvent |
| USAGE_SAVED_QUERY | config:usageSavedQuery |
| integration | |
| INTEGRATION_CONFIG | integration:integrationConfig |
| INTEGRATION_CREDENTIALS | integration:integrationCredentials |
| INTEGRATION_DESTINATION | integration:integrationDestination |
| INTEGRATION_RUN | integration:integrationRun |
| INTEGRATION_MARKETPLACE_USAGE | integration:marketplaceUsage |
| measurements | |
| MEASUREMENTS | measurements:data |
| MEASUREMENTS_VALIDATION_ERRORS | measurements:validationErrors |
| statement | |
| STATEMENT | statement:statement |
| statement definition | |
| STATEMENT_DEFINITION | statementdefinition:statementdefinition |
| statement job | |
| STATEMENT_JOB | statementjob:statementjob |
| exports | |
| EXPORTS_JOB | exports:data |
Creating Custom Permission Policies
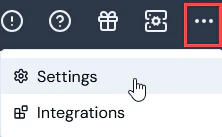
In the Settings area of the Console, you can quickly create and mange Custom Permission Policies. To create and manage Permission Policies:- Select Settings>Access settings:
- Select the Permission policies tab:
- Any system-generated Managed Permission Policies will be listed. You can view this type of Permission Policy and assign them to your Users, but you cannot edit them.
- Any Custom Permission Policies already created for your Organization are also listed and you can view and edit these.
- Select Create permission policy. The Create page opens.
- Under Permission policy details, enter a descriptive Name for the new Permission Policy.
- Under Permission policy statements, you have the option to use either a Simple or Advanced editor to add Statements to the Permission Policy. The Simple editor is selected by default.
- Leave the Simple editor selected. Here’s an example of how to compile Statements using the Advanced editor to allow all actions for all Meters:
- Under Effects, leave the default selection as Allow.
- Under Actions, select the All Config checkbox for Create, Retrieve, Update, and Delete.
- Under Resources, select Selected resources and use the drop-down to select
config.meter:

- Select Advanced if you want to add JSON formatted Statements. The page adjusts again to show a Statements text editor. Here’s an example of how to compile Statements using the Advanced editor to allow all actions for all Meters:

- If you want to add another JSON formatted Statement, select Add. A new Statement text editor window is shown:

- In addition to adding the specific** Permission policy statements** for a Custom Permission Policy, to ensure any Users who are assigned this as a single Permission Policy you must also add a Statement that enables these Users to access the m3ter Console. This Statement should allow them to Retrieve two Resources:
config:organizationConfigbilling:config
- When you have finished adding all of the required Statements for the Permission Policy, select Create permission policy. The Permission policy details page opens for the new Permission Policy:

- The new Permissions Policy is now available for assigning to Users, Service Users, and User Groups that have access to your Organization.
- Select Edit to edit the new policy.
- If you want to delete a Permission Policy, return to the Permission policies tab and select the delete icon for the Policy:

- Select Yes to confirm the delete.
Permissions Exceptions
There are instances where exceptions to the general permissions framework can occur as a result of shared data:- For example, if a user has been assigned a Permission Policy that denies them access to Products but grants them access to Bills, when they open a Bill, some Product data referenced by the Bill’s line items will be shown for the user.

